Morris Worm (1988): The Incident That Gave Birth to Cybersecurity
Before ransomware, nation-state attacks, and billion-dollar data breaches, there was a single experiment that changed everything. In late 80s, when…
Read More
How Your Wi-Fi Could Be an Open Door for Hackers
We all rely on Wi-Fi every day. At home, in cafés, at airports, in offices, and even on public transport,…
Read More
The Evolution of Cybersecurity: From Simple Defenses to AI-Powered Protection
Cybersecurity has come a long way since the early days of computing. What began as basic protective measures has now…
Read More
WannaCry: The Ransomware That Shook the World and Redefined Cybersecurity
In May 2017, a cyberattack erupted that would become one of the most notorious in history. Known as WannaCry, this…
Read More
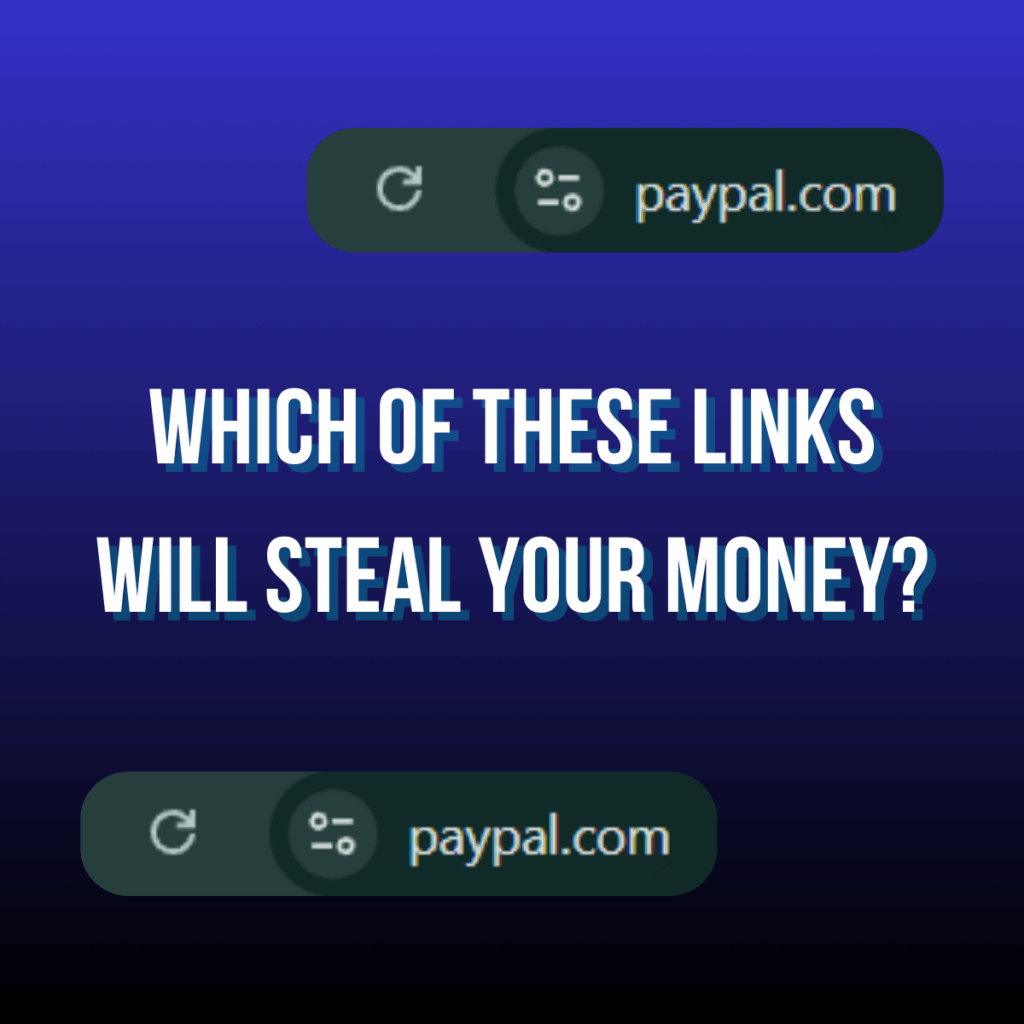
Cybersecurity Insights – One of these Identical Links Will Steal Your Data
Different tricks to Steal Your Information by using typography / Cybersecurity insights One of the most effective techniques used by…
Read More
New Android Trojan “Sturnus” Quietly Captures Encrypted Chats and Hijacks Devices
A newly identified Android trojan known as Sturnus is rapidly gaining attention within the cybersecurity community due to its sophistication…
Read More
Cybersecurity Neglect: The Cost of Ignoring Digital Security
Why Cybersecurity Neglect is a Growing Concern In today’s hyperconnected world, cybersecurity neglect is one of the biggest threats to…
Read More
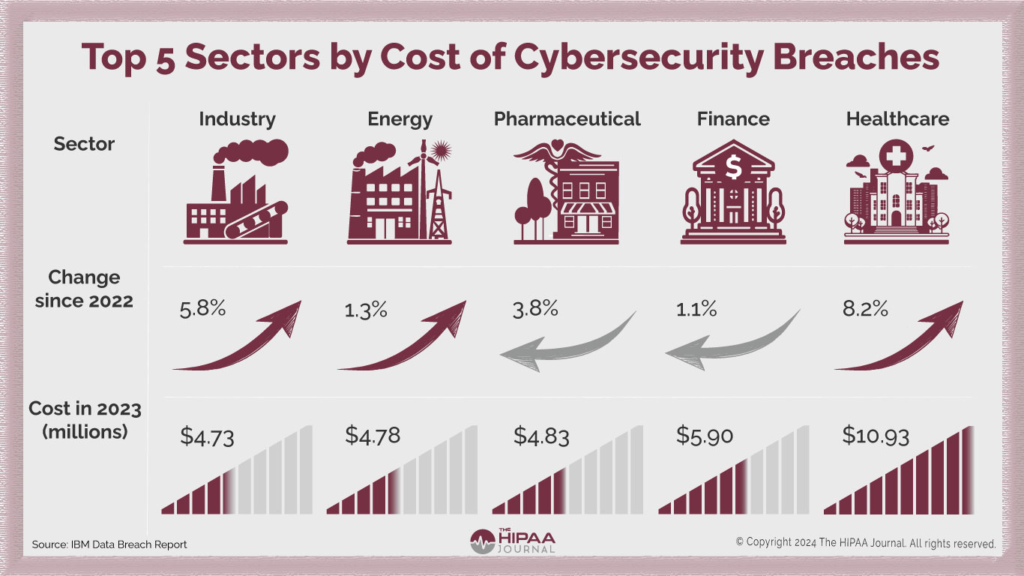
The Cost of Cybersecurity Breaches: What Businesses Need to Know
In today’s digital age, cybersecurity breaches are not only more common but more costly. Businesses of all sizes face the…
Read More
Understanding Passkeys and Adversary-in-the-Middle (AitM) Phishing Attacks
As digital security evolves, so do the tactics of cybercriminals. Despite advancements in authentication technologies, vulnerabilities still exist. One such…
Read More
Major Cyber Attacks, Data Breaches, and Ransomware Incidents in June 2024
June 2024 has been a turbulent month in the realm of cybersecurity, with several high-profile cyber attacks, data breaches, and…
Read More